An API key is a unique string that's used to route requests to your Firebase project when interacting with Firebase and Google services. This page describes basic information about API keys as well as best practices for using and managing API keys with Firebase apps.
General information about API keys and Firebase
API keys for Firebase are different from typical API keys
Unlike how API keys are typically used, API keys for Firebase services are not used to control access to backend resources; that can only be done with Firebase Security Rules (to control which end users can access resources) and Firebase App Check (to control which apps can access resources).
Usually, you need to fastidiously guard API keys (for example, by using a vault service or setting the keys as environment variables); however, API keys for Firebase services are OK to include in code or checked-in config files.
Although API keys for Firebase services are safe to include in code, you should review and apply appropriate restrictions and limits to them.
Creating API keys
A Firebase project can have many API keys, but each API key can only be associated with a single Firebase project.
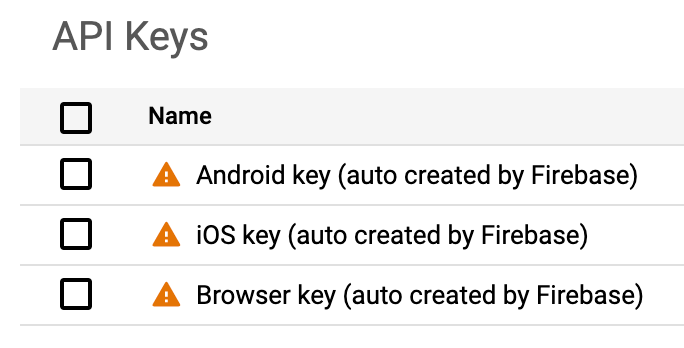
Firebase automatically creates API keys for your project when you do any of the following:
- Create a Firebase project >
Browser keyauto-created - Create a Firebase Apple App >
iOS keyauto-created - Create a Firebase Android App >
Android keyauto-created
You can also create your own API keys in the Google Cloud console, for example for development or debugging. Learn more about when this might be recommended later on this page.
Finding your API keys
You can view and manage all your project's API keys in the APIs & Services > Credentials panel in the Google Cloud console.
You can also find which API key is automatically matched to a Firebase App in the following places. By default, all of your project's Firebase Apps for the same platform (Apple vs Android vs Web) will use the same API key.
Firebase Apple Apps — Find the auto-matched API key in the Firebase config file,
GoogleService-Info.plist API_KEYfield.Firebase Android Apps — Find the auto-matched API key in the Firebase config file,
google-services.json current_keyfield.Firebase Web Apps — Find the auto-matched API key in the Firebase config object, in the
apiKeyfield.
Using an API key
API keys are used to identify your Firebase project when interacting with Firebase/Google services. Specifically, they're used to associate API requests with your project for quota and billing. They're also useful for accessing public data.
For example, you can explicitly use an API key by passing its value into a REST API call as a query parameter. This example shows how you might make a request to the Dynamic Links link shortener API:
POST https://firebasedynamiclinks.googleapis.com/v1/shortLinks?key=API_KEY
When your app makes a call to a Firebase API that requires an API key provided by the mobile/web client, your app will automatically look in the Firebase config file/object for your project's API key. You can, however, provide API keys for your app using a different mechanism, including environment variables.
Review and apply appropriate restrictions to API keys (recommended)
Although it's not necessary to treat an API key for Firebase services as a secret, you should review and apply restrictions and limits as described in this section.
Review the APIs automatically added to the allowlist for your Firebase API keys
When Firebase creates an API key in your project, we automatically add "API restrictions" to that key. The APIs added to this allowlist are Firebase-related APIs that require the client to provide an API key along with the call. Note that most APIs required for use of Firebase services don't actually need to be on the allowlist for your API keys.
Since Firebase adds the necessary APIs for all Firebase services, the allowlist for an API key may include APIs for products that you do not use. You can remove APIs from the allowlist, but you must be very careful to not remove the APIs required for Firebase and the Firebase services that you use (see the list of the Firebase-related APIs that need to be on the allowlist for each service / product). Otherwise, you will get errors when making calls to Firebase services.
Tighten quota if you use password-based Authentication
If you use password-based Firebase Authentication and someone gets hold of your API key, they will not be able to access any of your Firebase project's database or Cloud Storage data as long as this data is protected by Firebase Security Rules. They could, however, use your API key to access Firebase's authentication endpoints and make authentication requests against your project.
To mitigate against the possibility that someone might misuse an API key to
attempt a brute force attack, you can tighten the default quota of the
identitytoolkit.googleapis.com endpoints to reflect the normal traffic
expectations of your app. Be aware that if you tighten this quota and your app
suddenly gains users, you might get sign-in errors until you increase the quota.
You can change your project's API quotas in the
Google Cloud console.
Use separate, restricted API keys for any non-Firebase service
Although API keys used for Firebase services do not generally need to be treated as secret, you should take some extra precautions with API keys that you use with other Google Cloud APIs.
If you use a Google Cloud API (on any platform) that's not for a Firebase service / product, we strongly recommend creating separate, restricted API keys for use with those APIs. This is particularly important if the API is for a billable Google Cloud service.
For example, if you use Firebase ML and the Cloud Vision APIs on iOS, you should create separate API keys that you use only for accessing the Cloud Vision APIs.
By using separate, restricted API keys for non-Firebase APIs, you can rotate or replace the keys when necessary and add additional restrictions to the API keys without disrupting your use of Firebase services.
These instructions describe how to create a separate, restricted API key for a
fake API called Super Service API.
Step 1: Configure your existing API keys to disallow access to Super Service API
Open the Credentials page of the Google Cloud console. When prompted, select your project.
For each existing API key in the list, open the editing view.
In the API restrictions section, select Restrict key, then add to the list all of the APIs to which you want the API key to have access. Make sure to not include the API for which you're creating a separate API key (in this example,
Super Service API).When you configure an API key's API restrictions, you are explicitly declaring the APIs to which the key has access. By default, when the API restrictions section has Don't restrict key selected, an API key can be used to access any API that is enabled for the project.
Now, your existing API keys will not grant access to Super Service API, but
each key will continue to work for any APIs that you added to its
API restrictions list.
Step 2: Create and use a new API key for access to Super Service API
Return to the Credentials page. Be sure your Firebase project is still selected.
Click Create credentials > API key. Take note of the new API key, then click Restrict key.
In the API restrictions section, select Restrict key, then add to the list only the
Super Service API.This new API key grants access only to the
Super Service API.Configure your app and services to use the new API key.
Use environment-specific API keys (recommended)
If you set up different Firebase projects for different environments, such as staging and production, it's important that each app instance interacts with its corresponding Firebase project. For example, your staging app instance should never talk to your production Firebase project. This also means that your staging app needs to use API keys associated with your staging Firebase project.
To reduce problems promoting code changes from development to staging to production, instead of including API keys in the code itself, either set them as environment variables or include them in a configuration file.
Note that if you're using the Firebase Local Emulator Suite for development along with Firebase ML, you must create and use a debug-only API key. Instructions for creating that kind of key are found in the Firebase ML docs.
FAQs and troubleshooting
FAQs
Yes, by default, all API keys that Firebase auto-provisions for use with Firebase-related APIs have "API Restrictions" applied automatically. See the list of the Firebase-related APIs that are on this allowlist.
The APIs added to this allowlist are those APIs called by Firebase services from client-code and require API keys for identification of your Firebase project or app. Note that most APIs required for use of Firebase services don't actually need to be on the allowlist for your API keys.
Since Firebase adds the necessary APIs for all Firebase services, the allowlist for an API key may include APIs for products that you do not use. You can remove APIs from the allowlist, but you must be very careful to not remove the APIs required for Firebase and the Firebase services that you use (see the list of the Firebase-related APIs that need to be on the allowlist for each service / product). Otherwise, you will get errors when making calls to Firebase services.
You can view all your API keys and their "API restrictions" in the APIs & Services > Credentials panel in the Google Cloud console.
Note the following about how Firebase applies these "API restrictions":
Starting in May 2024, all new API keys auto-provisioned by Firebase are automatically restricted to the list of the Firebase-related APIs.
During May 2024, all existing and unrestricted API keys that Firebase had previously auto-provisioned are restricted to the list of the Firebase-related APIs plus any of the project's currently enabled APIs.
Any existing and already restricted API keys that Firebase had previously auto-provisioned were not changed.
Any existing API keys that were not auto-provisioned by Firebase were not changed.
You can use any of the following options to determine which API key is associated with your Firebase App:
Firebase console
Go to Project settings, and then scroll down to the Your apps card.
Select the app of interest.
Obtain the Firebase config file/object for the app of interest, and then find its API key:
Apple: Download the
GoogleService-Info.plist, and then find theAPI_KEYfieldAndroid: Download the
google-services.json, find the config for the app of interest (look for its package name), and then find thecurrent_keyfieldWeb: Select the Config option, and then find the
apiKeyfield
Firebase CLI
Obtain the Firebase config file/object for the app of interest by running the following command:
firebase apps:sdkconfig PLATFORM FIREBASE_APP_ID
- PLATFORM (one of):
IOS|ANDROID|WEB - FIREBASE_APP_ID: the Firebase-assigned unique identifier for your Firebase App (find your App ID)
- PLATFORM (one of):
In the app's printed Firebase configuration, find its API key:
Apple: Find the
API_KEYfieldAndroid: Find the config for the app of interest (look for its package name), and then find the
current_keyfieldWeb: Find the
apiKeyfield
REST API
Obtain the
apiKeyId(the UID) of the API key by calling the applicable endpoint for the app of interest, and then passing theapiKeyIdvalue to the next step.- Apple: Call
projects.iosApps.get - Android: Call
projects.androidApps.get - Web: Call
projects.webApps.get
- Apple: Call
Obtain the API key string by calling
projects.locations.keys.getKeyString.This
keyStringis the same value that can be found in the App's configuration artifact (Apple | Android | Web).
Firebase Apple Apps — Each app has its own config file and can have only one API key listed.
Firebase Android Apps — All Android apps in the Firebase project are listed in the same config file, and each app can only have one API key listed. Each app in this config file can have a different key listed, though.
Firebase Web Apps — Each app has its own config object and can have only one API key listed.
You can use multiple API keys with one app, though. You must provide a mechanism for your app to access these other API keys, like via an environment variable. The mechanism to access the other API keys just can't depend on those API keys being listed in your Firebase config file/object.
When you first obtain your app's Firebase config file/object, Firebase checks if there are any existing API keys in your project that have "Application Restrictions" that match the app (for example, a matching bundle ID for the Apple app).
If Firebase doesn't find any restricted keys that match, then it will list in
the config file/object the iOS key for Apple apps, the Android key for
Android apps, and the Browser key for web apps (assuming that these keys exist
and have no "Application Restrictions" that keep them from matching to that
app).
Yes, you can manually delete your API key from your config file/object. However, you must provide some other mechanism for your app to access an API key (like via an environment variable). Otherwise, any calls to Firebase services will fail.
Yes, you can manually edit a config file/object to associate a different API key with an app.
Note that if you re-obtain your app's config file/object from the console, it will always list the API keys that Firebase automatically matches to that app. So, you'll need to repeat your manual edits, as needed.
No, an API key only identifies a specific project and cannot be moved to another project.
If you delete an API key that's in use by an app, then API calls from that app will fail. You may get reports, emails, or errors that you're attempting to use an API key that is invalid.
Deleting an API key is permanent and cannot be undone.
For a Firebase API key, the only APIs that need to be on the key's "API restrictions" allowlist are the APIs that require the client to provide an API key along with the call. Note that very few Firebase-related APIs have this requirement. Most Firebase-related APIs enabled in your project don't need to be on the key's "API restrictions" allowlist.
Use the following table to determine which Firebase-related APIs need to be included in the "API restrictions" allowlist for a Firebase API key. Remember, Firebase API keys should only be used for Firebase services. Learn more about creating separate, restricted API keys for specific types of APIs.
You can view and manage your project's API keys in the APIs & Services > Credentials panel in the Google Cloud console.
| API name (service name) | API display name | Associated Firebase service / product |
|---|---|---|
| firebase.googleapis.com | Firebase Management API | all products |
| logging.googleapis.com | Cloud Logging API | all products |
| firebaseinstallations.googleapis.com | Firebase Installations API | Cloud Messaging, Crashlytics, In-App Messaging, Performance Monitoring, Remote Config, Firebase ML |
| firebaseappcheck.googleapis.com | Firebase App Check API | App Check |
| firebaseappdistribution.googleapis.com | Firebase App Distribution API | App Distribution |
| firebaseapptesters.googleapis.com | Firebase App Testers API | App Distribution |
| identitytoolkit.googleapis.com | Identity Toolkit API | Authentication |
| securetoken.googleapis.com | Token Service API | Authentication |
| firebaserules.googleapis.com * | Firebase Rules API | Cloud Firestore, Cloud Storage, Realtime Database |
| datastore.googleapis.com | Cloud Datastore API | Cloud Firestore |
| firestore.googleapis.com | Google Cloud Firestore API | Cloud Firestore |
| fcmregistrations.googleapis.com | FCM Registration API | Cloud Messaging |
| firebasestorage.googleapis.com | Cloud Storage for Firebase API | Cloud Storage |
| firebasedynamiclinks.googleapis.com | Firebase Dynamic Links API | Dynamic Links |
| firebasehosting.googleapis.com * | Firebase Hosting API | Hosting |
| firebaseinappmessaging.googleapis.com | Firebase In-App Messaging API | In-App Messaging |
| firebaseml.googleapis.com | Firebase ML API | Firebase ML, Vertex AI for Firebase |
| mlkit.googleapis.com ** | ML Kit API | Firebase ML |
| mobilecrashreporting.googleapis.com | Mobile Crash Reporting API | Performance Monitoring |
| play.googleapis.com | Google Play Android Developer API | Performance Monitoring |
| firebaseremoteconfig.googleapis.com | Firebase Remote Config API | Performance Monitoring, Remote Config |
| firebaseremoteconfigrealtime.googleapis.com | Firebase Remote Config Realtime API | Performance Monitoring, Remote Config |
| cloudconfig.googleapis.com ** | N/A | Remote Config |
| firebasedatabase.googleapis.com * | Firebase Realtime Database API | Realtime Database |
* Required only if you're using the Firebase API key with third-party tools or direct REST access to the Firebase service / product.
** Required for earlier versions of the product's SDK. If you're using the latest version of the SDK, the API doesn't need to be on the key's allowlist.
Troubleshooting
Follow the guidance in this FAQ if you're getting a API_KEY_SERVICE_BLOCKED
error or an error that looks like the following:
Forbidden: 403 POST https://example-service.googleapis.com/method: Requests to this API example-service.googleapis.com method google.example-service.rest.method are blocked.
The API key used by your app to call the API probably has "API Restrictions" applied to it, and the key's allowlist doesn't include that API.
If you're getting this error when trying to use a Firebase-related service / product, then make sure that the API key that you're using has all the required APIs included in the key's "API restrictions" allowlist.
If you're getting this error when trying to use a non-Firebase service, then we strongly recommend creating a new API key specifically for that service and API. Firebase API keys should only be used for Firebase services / products. Learn more about creating separate, restricted API keys for specific types of APIs.
The API key used by your web app probably has "API Restrictions" applied to it. If this is the case, make sure that the Firebase Management API is in the list of allowed APIs.
Here are a few of the most common causes for invalid API keys:
The API key has "API Key Restrictions" applied to it that make it unmatchable to the app attempting to use the key ("Application Restrictions") or unusable for the API being called ("API Restrictions").
The API key was deleted from the project in the Google Cloud console.
The API key was not created for the Project ID listed in the app's Firebase config file/object.
One way to fix this issue is to obtain the updated version of your app's Firebase config file/object, then replace your old config file/object with the new updated file/object. Before sending a config file for download or displaying a config object in the console, Firebase checks that the API key(s) listed match to the app(s).
